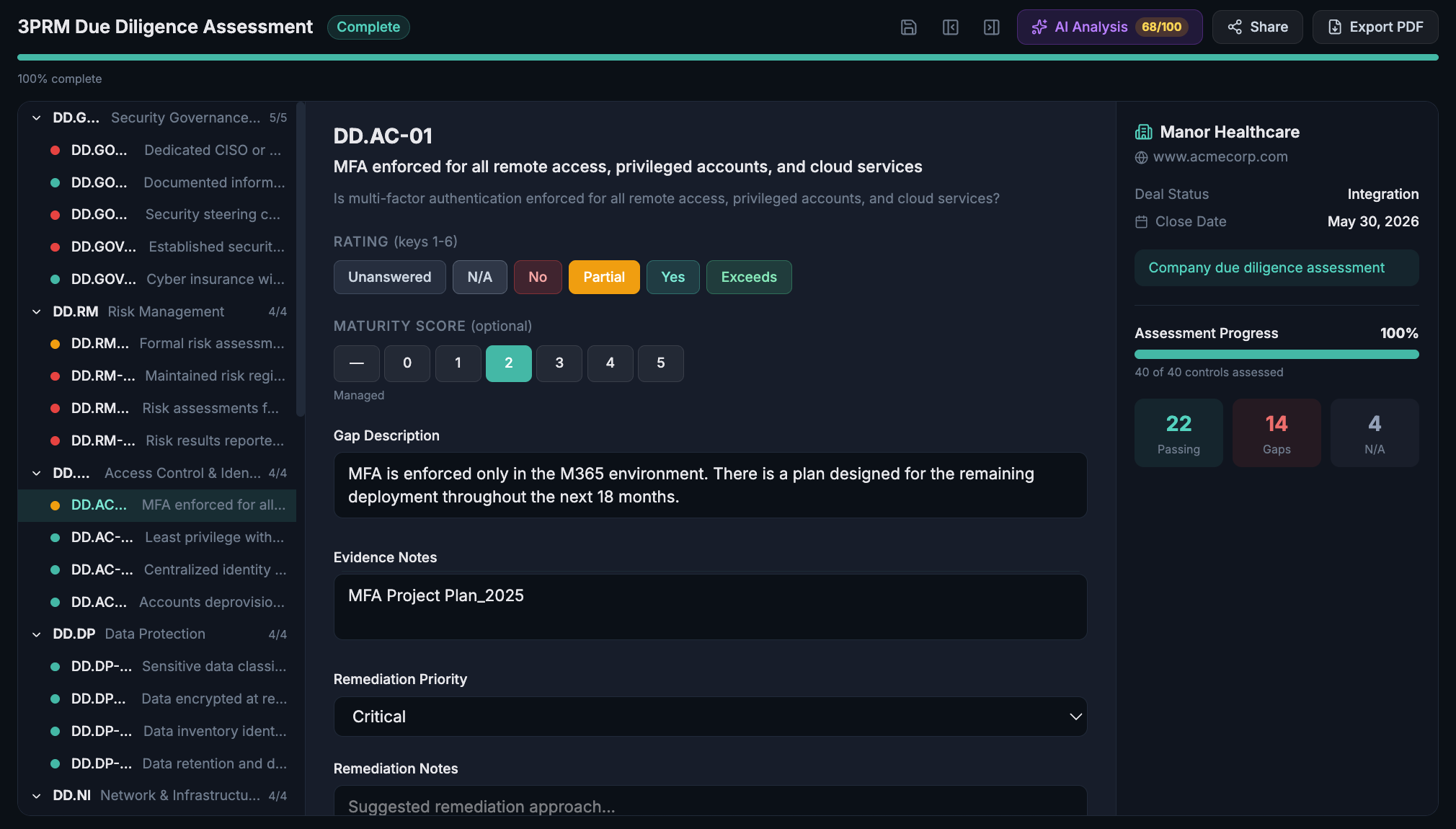
Control-by-control assessment with AI scoring
Structured assessments mapped to the frameworks that matter. Rate each control, capture evidence, describe gaps, and get an AI-powered composite score, all in one place.
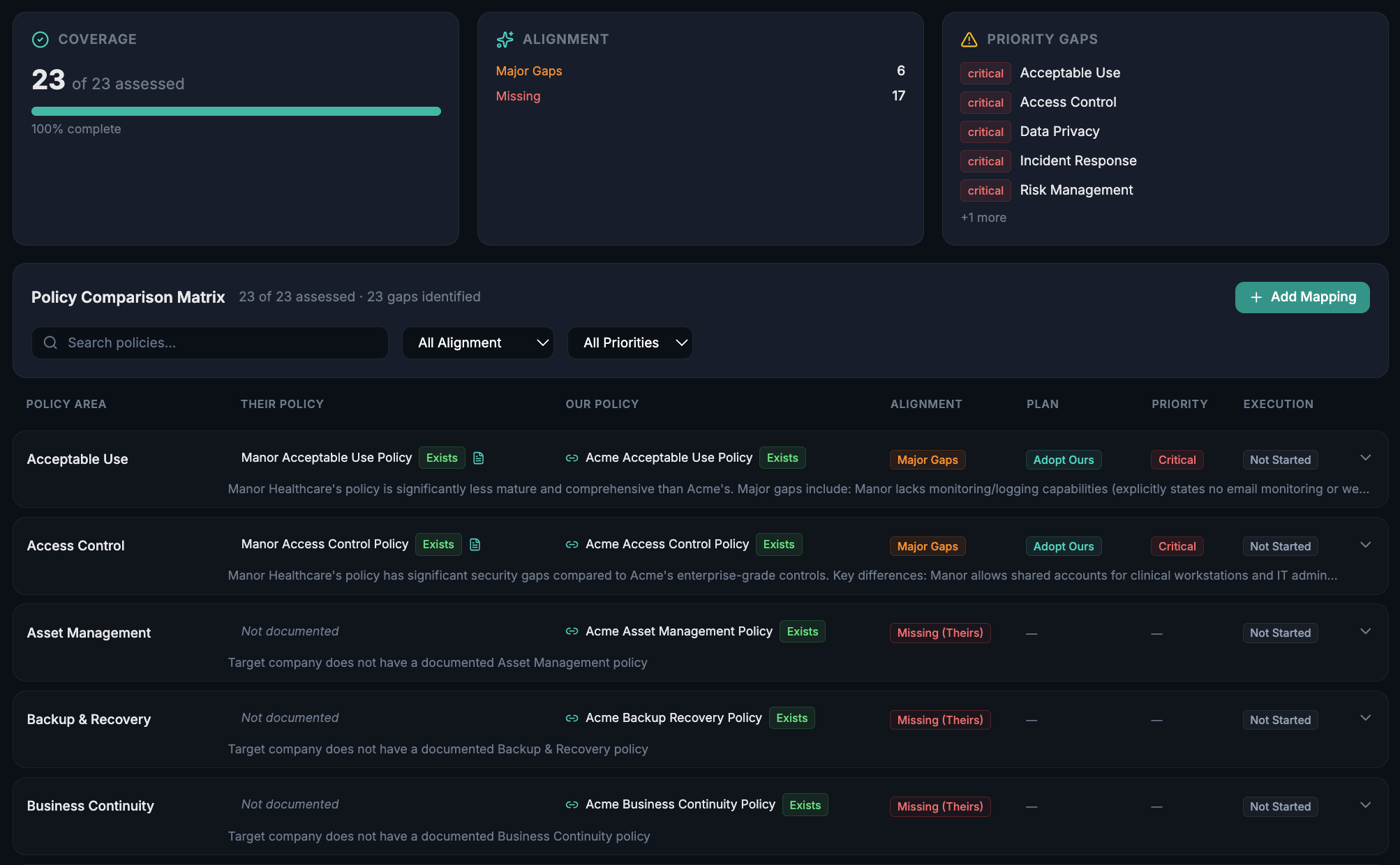
Know exactly what you're inheriting
Side-by-side comparison of the target's policies against your own. Instantly see alignment gaps, missing policies, and critical areas requiring remediation before close.
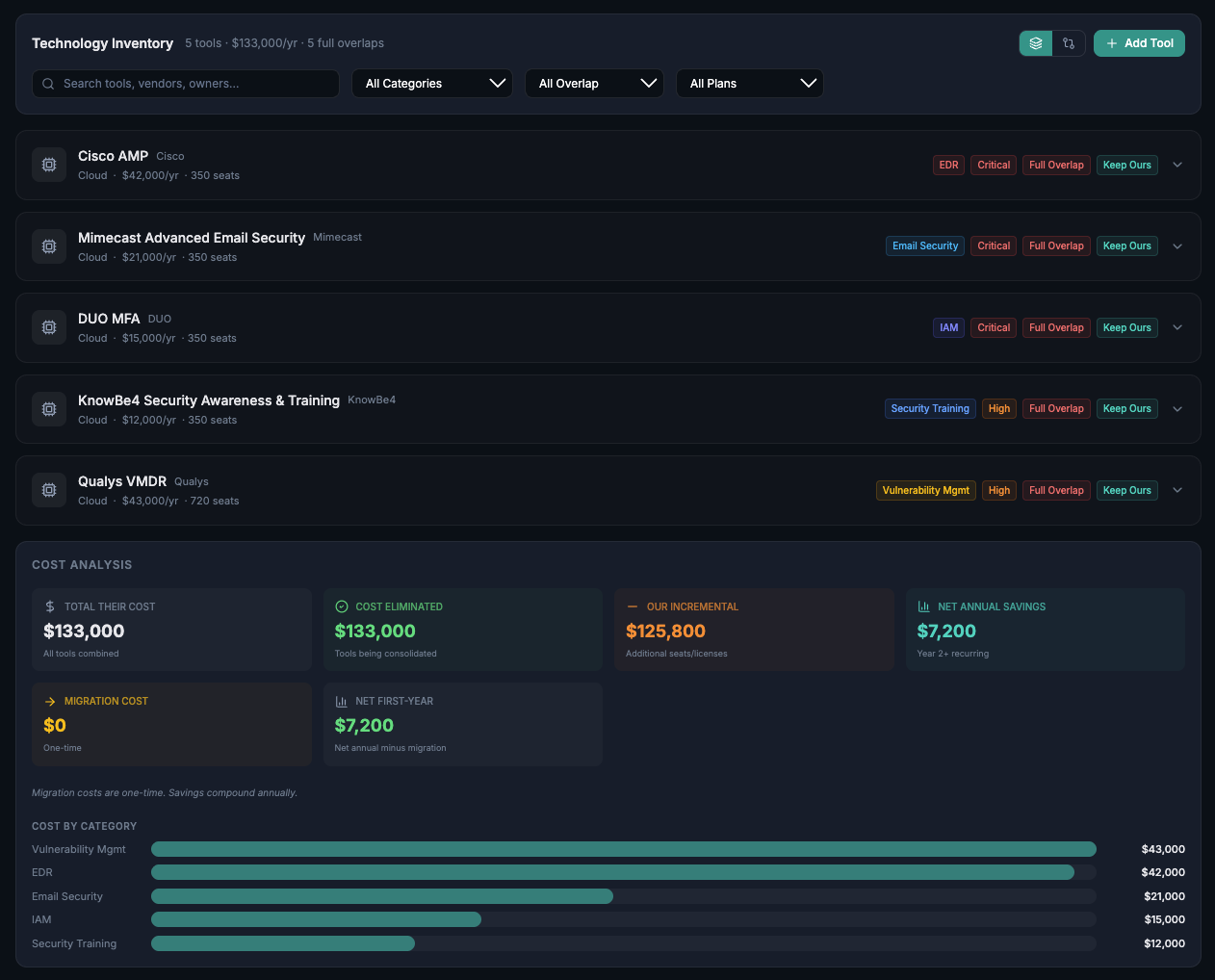
Quantify the integration cost before you sign
Inventory every tool the target runs, identify overlaps with your stack, and get a clear picture of consolidation savings and integration costs.
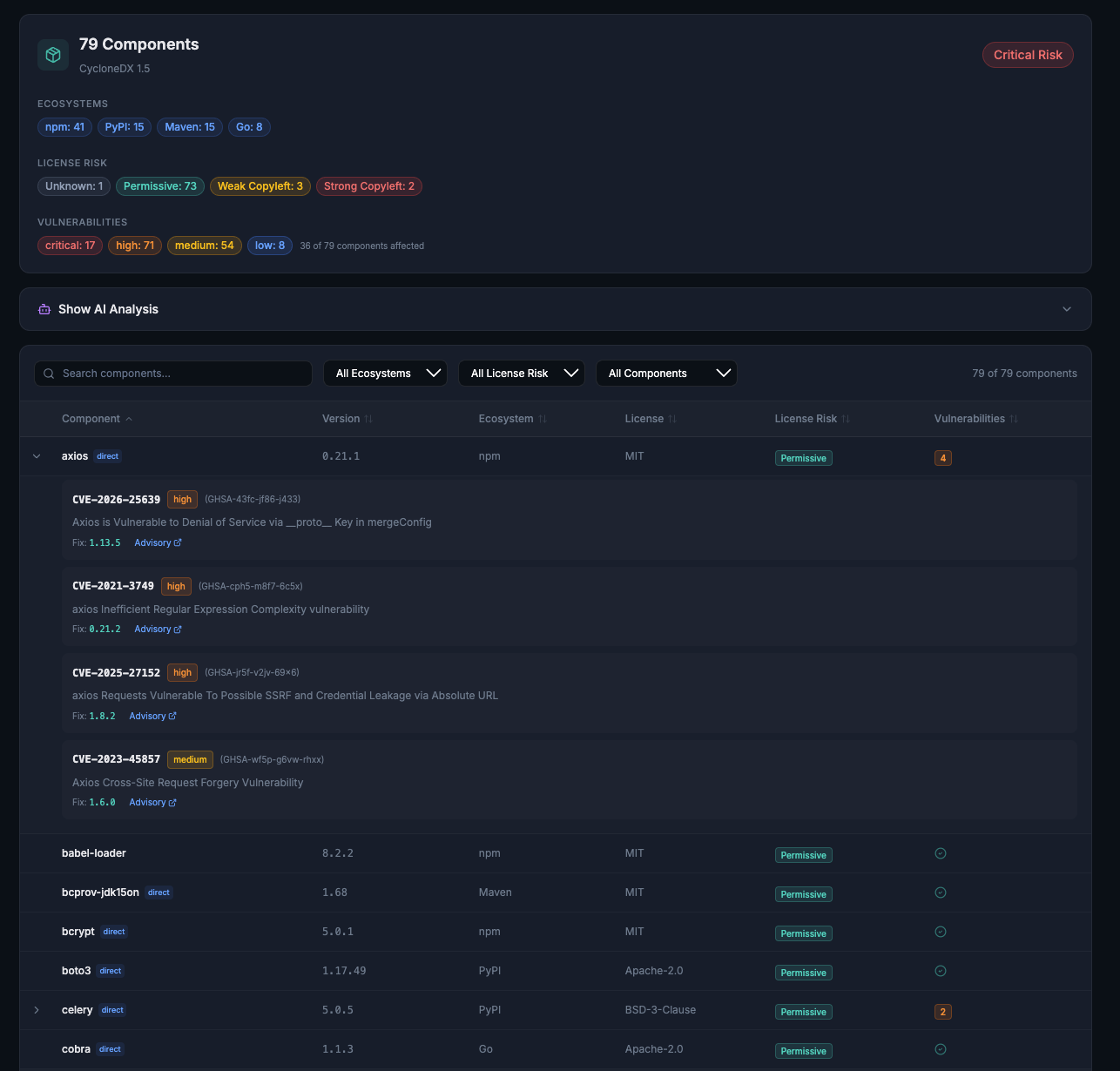
See the software risk you'd be acquiring
Upload a SBOM and get instant CVE analysis across every component. License risk classification, vulnerability severity breakdown, and AI-powered findings.
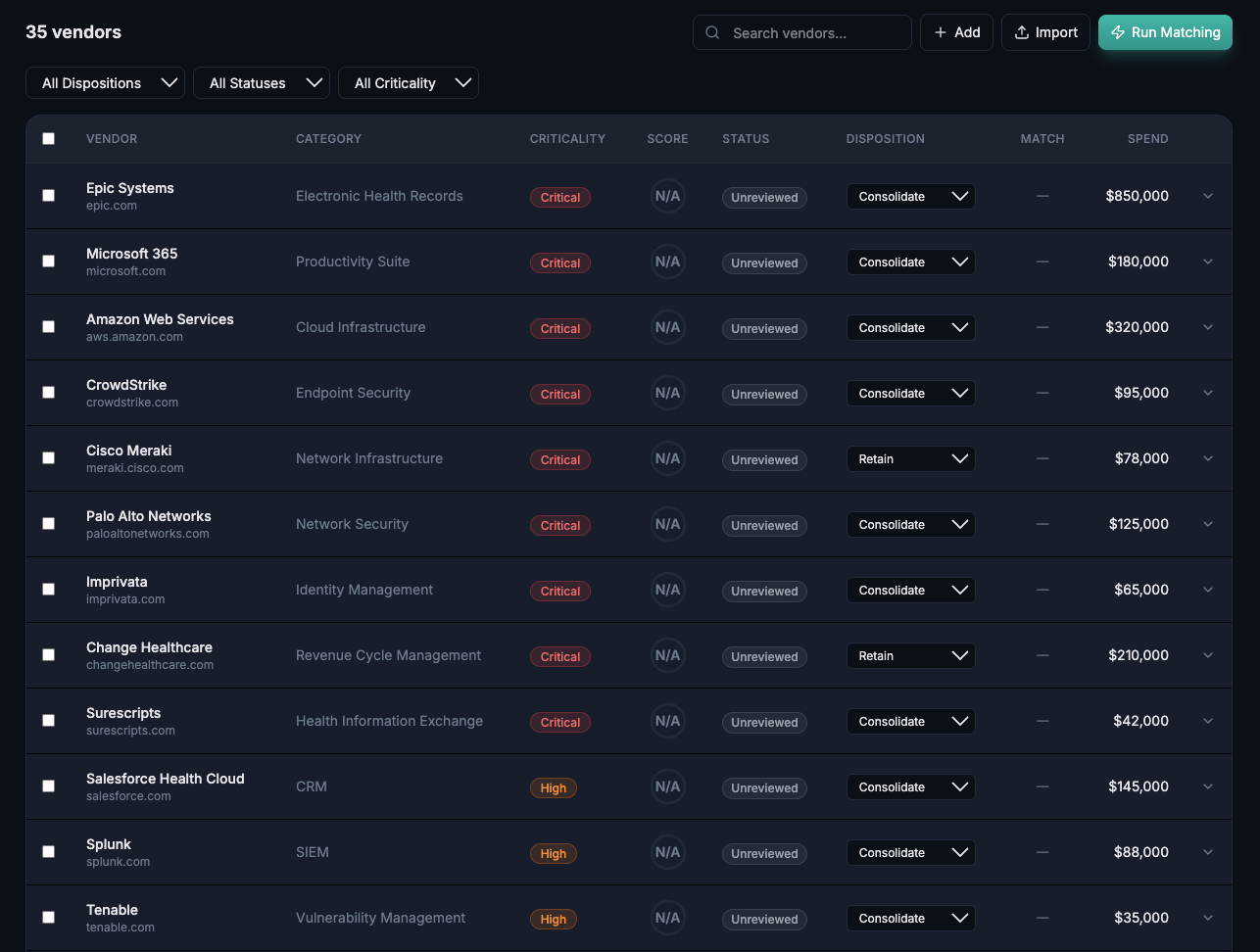
Understand the vendors you're inheriting
The target's third-party relationships become yours at close. Map every inherited vendor, assess criticality, and make disposition decisions before integration begins.
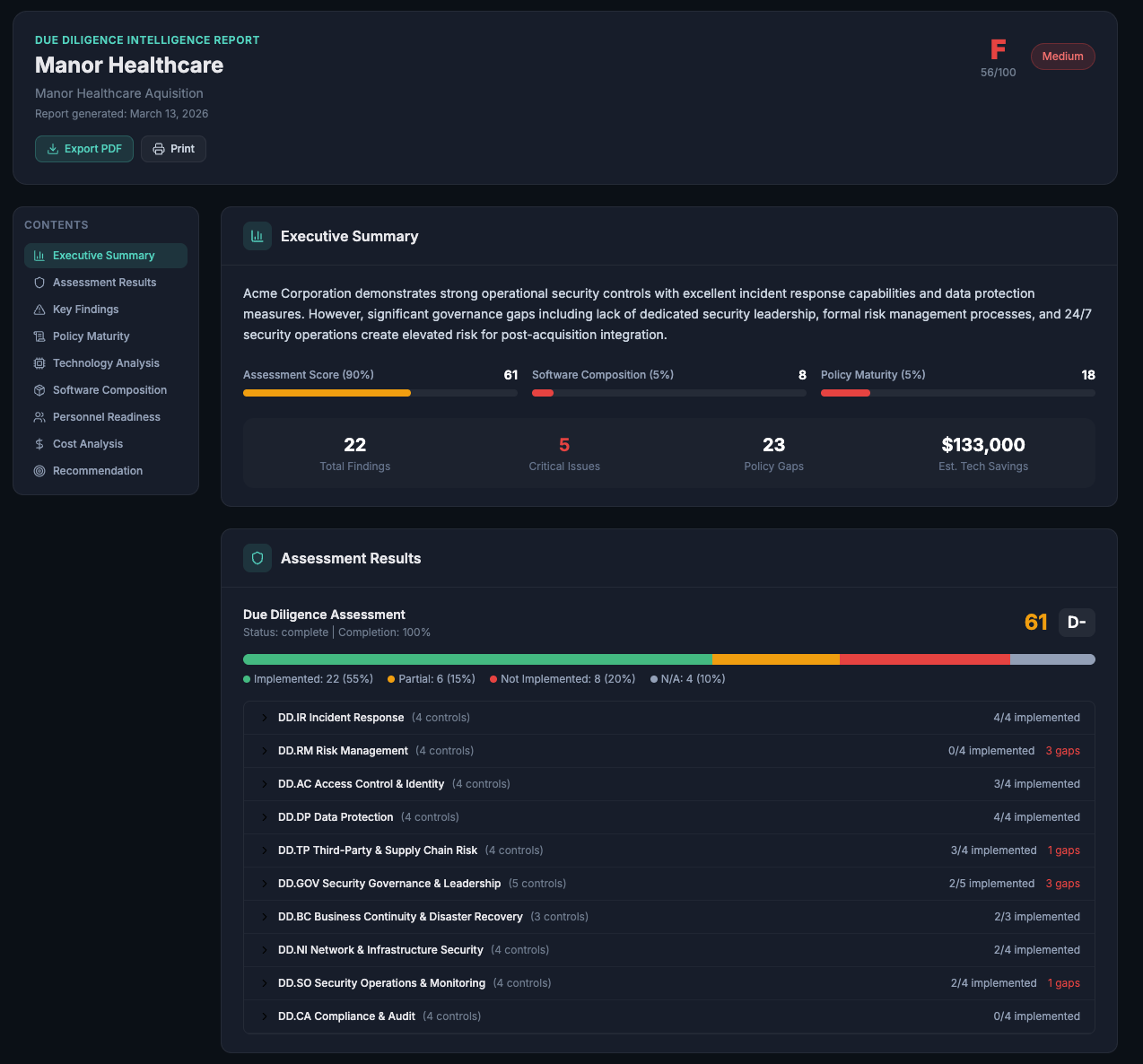
Assessment to investment committee in one click
Generate a DD Intelligence Report with composite scoring, weighted risk components, executive summary, and full findings detail. The artifact your CISO hands to the board.
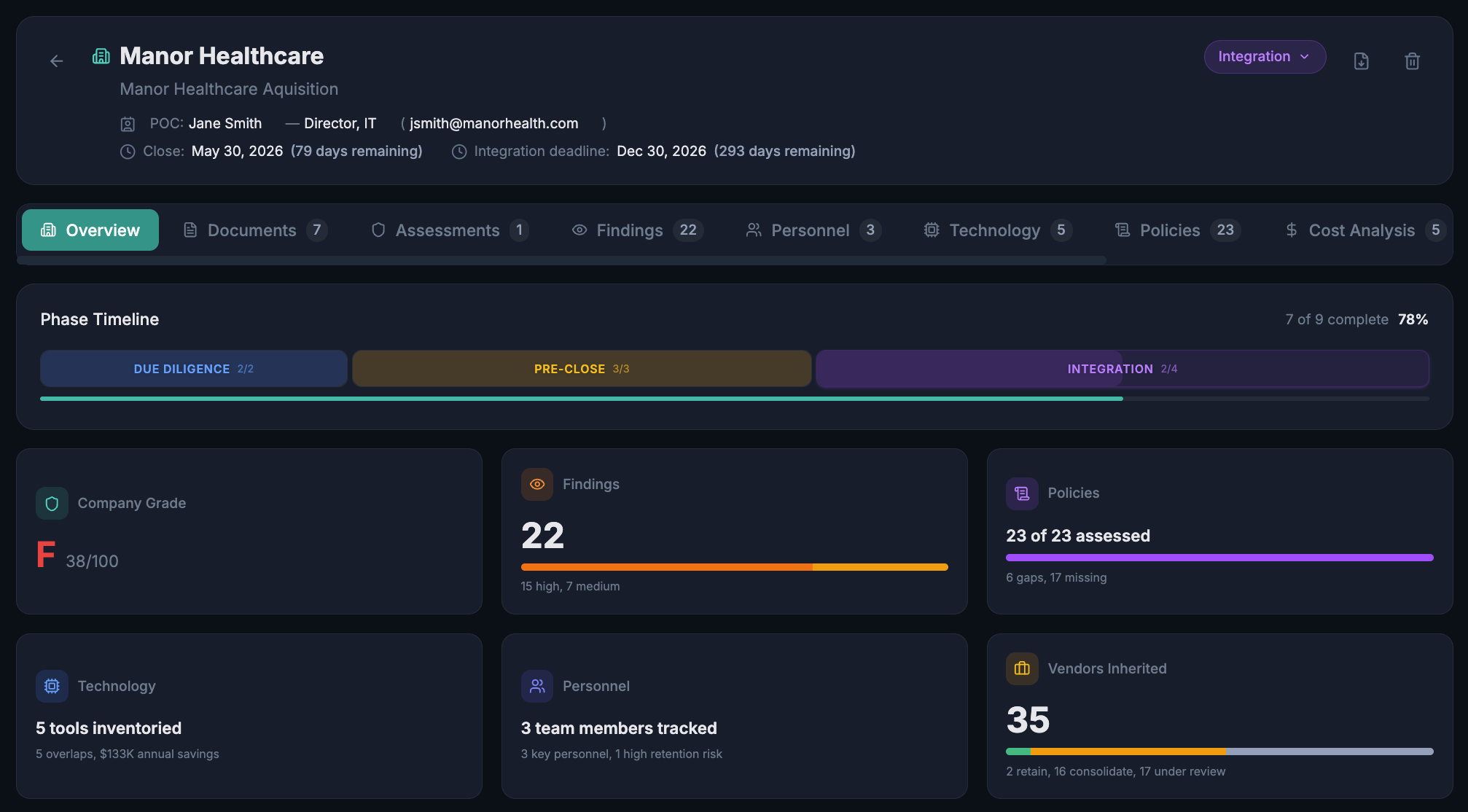
One platform for the full deal lifecycle
Built by a CISO who's been on both sides of the table
3PRM was built by a practicing CISO who has sat on both sides of the M&A table. Every feature exists because it was needed in a real deal.